JUST RELEASED: Microsoft Defender for Identity Release 2.198: Improved User Timeline, Automated Attack Disruption, and More!
🔥JUST RELEASED: Microsoft Defender for Identity Release 2.198: Improved User Timeline, Automated Attack Disruption, and More!🔥
Microsoft recently released Defender for Identity 2.198, which includes several new features and improvements.
Microsoft recently released Defender for Identity 2.198, which includes several new features and improvements.
✔️The updated User page in Microsoft 365 Defender now has a new look and feel, with an expanded view of related assets and a new dedicated timeline tab.
✔️The timeline represents activities and alerts from the last 30 days, and it unifies the user’s identity entries across all available workloads (Defender for Identity/Defender for Cloud Apps/Defender for Endpoint). By using the timeline, you can easily focus on activities that the user performed (or were performed on them), in specific timeframes.
✔️The honeytoken activity alert has been split into five separate alerts, with exclusions added to provide a customized experience for the user's environment.
✔️Microsoft has also introduced a new security alert for suspicious certificate usage over Kerberos protocol (PKINIT). This behavioral monitoring approach alerts users when it observes suspicious certificate usage, providing comprehensive protection against AD CS attacks.
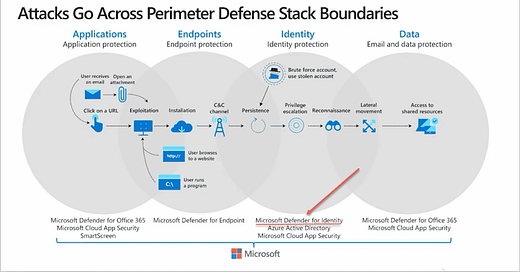
✔️Defender for Identity now works together with Microsoft 365 Defender to offer Automated Attack Disruption. This means that, for signals coming from Microsoft 365 Defender, analysts can trigger the Disable User action. The action suspends the compromised user account in Active Directory and syncs this information to Azure AD. Users can also exclude specific users from the automated response actions.
✔️The alerts generated by Defender for Identity are based on various factors such as profiling, deterministic detection, machine learning, and behavioral algorithms that it has learned about the user's network. The full learning process for Defender for Identity can take up to 30 days per domain controller. However, admins can turn off the learning period for the affected alerts by enabling the Remove learning period feature.
✔️Finally, Microsoft has announced that all Defender for Identity experiences will be available in the Microsoft 365 Defender portal, and the primary alert pipeline will be switched from "Defender for Identity > Defender for Cloud Apps > Microsoft 365 Defender" to "Defender for Identity > Microsoft 365 Defender". This change should significantly reduce the time it takes for alerts to appear in the Microsoft 365 Defender portal. The version also includes improvements and bug fixes for internal sensor infrastructure.
Want to learn more? 💡 📝MS docs: https://lnkd.in/eWWsthzr